According to a recent report from the research firm IDC entitled Data Age 2025, more than 33 zettabytes of data were generated in 2018. (A zettabyte is one sextillion bytes – or 1000 to the 7th power) Within seven years IDC predicts that number will explode to an incredible 175 zettabytes, with more than 30 percent of that data requiring real-time processing. Where will all this data be held, processed, and stored?
This explosive growth in data is rapidly changing how organizations approach data use, storage and security. In the past, data architects assumed that data centers were actual buildings, in fixed locations, and that traditional security controls could be applied to protect it. This is at least partially true for today’s conventional central data centers, hyperscale facilities, and colocation centers, that need both physical and cyber security protections. One challenge with these centralized facilities is that while they have the computing power to support analytics, machine learning, and other advanced processing tasks, they can be long distances away from the users, leading to unacceptable latency delays that can decrease the value of those services.
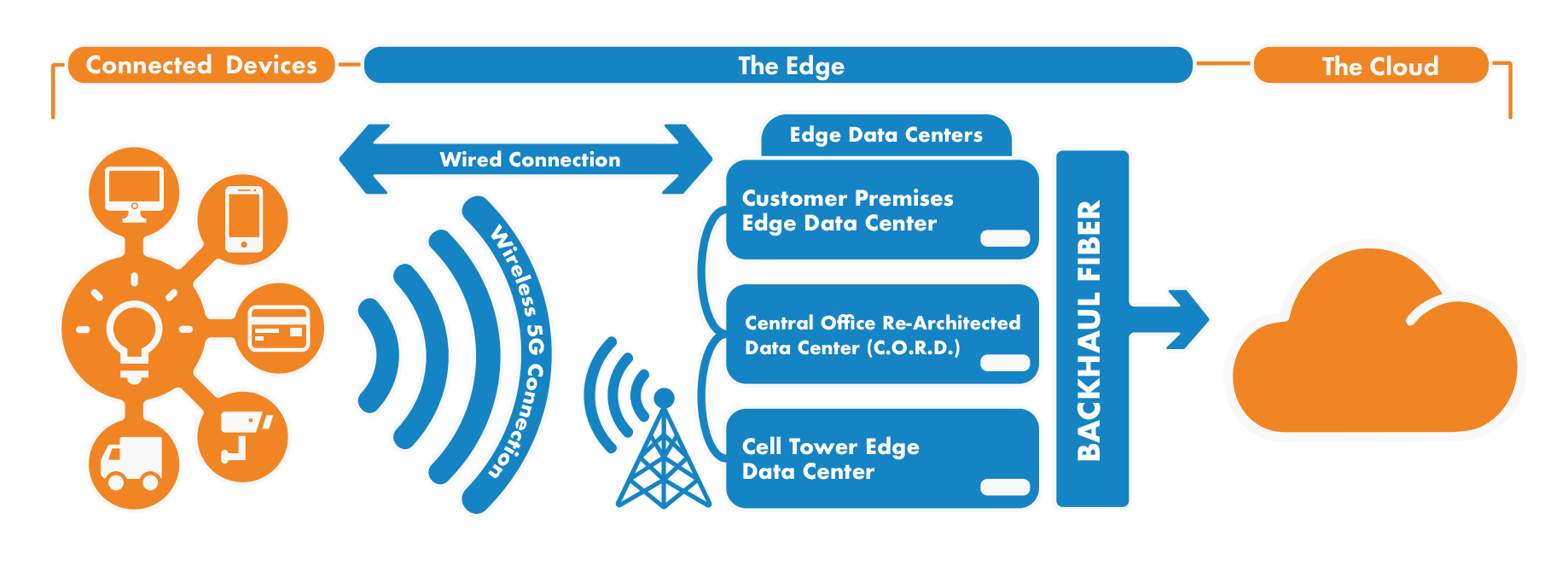
“Edge data centers” is a new idea that is gaining momentum and challenging the traditional architecture assumptions. Edge data centers are generally smaller facilities located remotely from central data centers, extending the edge of the network to deliver cloud computing resources and cached streaming content to local end users. While they provide a variety of services on their own, they are connected back to larger data centers that provide additional resources and processing when needed.
Global Market Insights is predicting that the edge data center market will grow at a CAGR of more than 20 percent between 2019 and 2024. This consistent drive to the edge means that the concept of the traditional data center will be transformed into many edge data center solutions. This change will in turn stretch the capabilities of providers to define adequate footprints, infrastructure, connectivity and security to address the ever-increasing demands.
New Requirements for a New Environment
Today, the edge is anywhere data gathers and intersects with its user’s location – and that can be almost anywhere as IoT expansion dots devices all along the technology roadmap. Gartner says that by 2025 we will see close to 75 percent of all data be analyzed at the edge. So, what will change with edge data centers, and what does this mean in the context of establishing a physical security strategy? Here are some areas that are experiencing significant change:
Cybersecurity: “Big box” data center standards and methods that were developed more than a decade ago don’t adequately address cybersecurity. Today, datacenters must consider seamless multifactor authentication and the increased importance of identity management and access rights to remain viable, and ongoing monitoring and management are crucial to protect organizational data. Automated management of firmware patches, passwords, and certificates are needed to handle the scale of keeping edge data centers cyber-secure.
Physical Security: The old paradigm that concentrated on protecting physical assets and people must now include data, intellectual property and operations. Video evidence from the perimeter of an edge data center can help track cyberattacks from initial reconnaissance. Edge data centers may have automated methods of maintenance (e.g. drone-based), which creates new requirements for access control.
Proactive Actions: The mindset for both physical and network security staff must assume an aggressive proactive risk mitigation stance instead of taking the rearview mirror approach of basing strategies on past events.
On-Demand, Real Time: The thirst for on-demand information and lightning-fast and real-time response is developing rapidly. As the edge expands to self-driving cars and personal medical devices, real-time and low-latency detection of failures will be absolutely required to avoid potentially life-threatening situations. Should such failures arise, the edge data center must be capable of moving its compute workload to an adjacent data center without disrupting critical functions like control of self-driving cars.
Remote Security: The historical security and maintenance functions that were previously centralized must now consider new mechanisms for remote capabilities, remote servicing and remote access. Edge data centers can now include any data device installed on a light pole, a cellular tower, or even a buried sensor in the ground, so physical security must become remote and remotely accessible through digital connections.
The ability to successfully secure edge data centers will ultimately depend on how each organization assesses their risks and priorities. A large global organization migrating from a handful of core data centers to thousands of edge centers will have to decide what their CAPX tolerance may be. As emerging technology continues to provide options, many consultants maintain that organizations should try to integrate technology with every data-related system deployment to maintain a proactive security stance whenever possible.